15 Top Cybersecurity Tools – Featuring Expert Insights
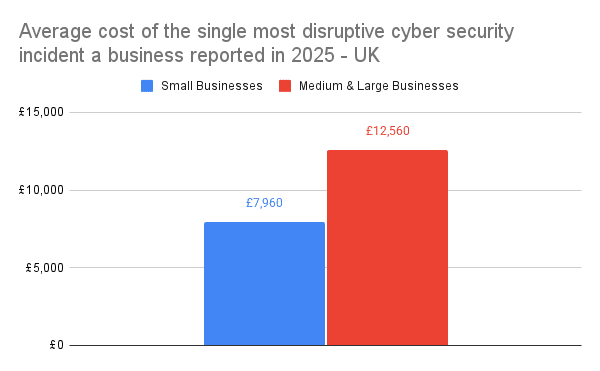
Cybersecurity is a business essential and a marketable asset, and proving a high level of cybersecurity is a requirement for working with any enterprise. And for good reason, according to a study published by the UK Government, successful cyber attacks cost the UK £14.7 billion annually, with 43% of businesses reporting a cybersecurity breach or attack in 2025.
Ignoring the huge costs of a security incident for a moment, data security is also a key factor in customer loyalty. How much would you trust a business which has had a data breach?
AI has been a huge power up for bad actors, allowing for stronger attacks at greater scale. The internet is more dangerous than ever, but it goes both ways. The AI security tools section of this article will show you some of the innovative new ways that your organisation can be on the forefront of security.
MeasureMinds are the data experts, and that includes keeping data secure. To help you with your security, we’ve spoken to industry experts as well as the tool creators themselves to compile a list of some of the best cybersecurity tools available, whether you’re an SMB, an enterprise, or a solo user.
We’ve also teamed up with the award-winning anti-virus Total AV to offer you a huge 80% off their premium protection, bringing the cost down to as little as £19 for the first year, exclusively available through our link. Premium packages also contain useful tools such as a VPN and iOS & Android protection. Click this link to get 80% off Total AV now.
All-in-one
Starting off with the heavy hitters, these total security platforms are behind some of the biggest enterprises.
Fortinet
Founded in 2000, Fortinet has the largest integrated offering available with a portfolio of over 50 enterprise-grade products.
Fortinet also offers dedicated protection for small to medium businesses, with analyst consultation and setup.
Key Benefits
- All-in-one security suite for enterprises and small businesses
- Practically guaranteed to solve all your security needs
- Reduces complexity
- Solutions tailored to your needs, so you won’t be paying for things you don’t need
- Industry-leading protection
Potential Downsides
- Cost
- While pricing can vary greatly, you can be fairly sure this won’t be the cheapest option available.
- Setups and changes may require engineers skilled in FortiOS, Fortinet’s own custom operating system.
- Teams with limited network/security expertise and requirements may prefer simpler, cloud-native tools.
- UI is often described as powerful but dated
- Fortinet is still hardware- and network-centric at its core
- Cloud security offerings, SaaS protection, and identity-centric security aren’t Fortinet’s strongest areas
Best suited for
Enterprises that want their full security needs met, or small businesses that aren’t cloud-focused.
Bitdefender
Founded in 2001, Bitdefender is a complete platform for individuals, small businesses, and enterprises.
Key Benefits
- Excellent core security
- Consistently top-tier detection and ransomware prevention in independent tests.
- Excellent dashboard and interface that scales well
- Single cloud console to manage endpoints, servers, email security, patching, etc.
- Strong feature set out of the box
- Many features that competitors charge extra for come as standard
- Good performance on endpoints
- Lightweight with minimal user disruption
- Generally good value
- For SMBs and Enterprises
Potential Downsides
- Setup and admin complexity
- Requires real IT and security skills to configure
- Some reports of slow support response
- Still not cheap
- Bitdefender is still a premium product, and pricing reflects that (especially at enterprise scale)
Best suited for
Small-to-medium organisations wanting easy-to-manage, affordable endpoint security.
Crowdstrike
Crowdstrike is an all-in-one Security Platform that’s cloud native and AI-powered.
Key Benefits
- Cloud-native & easy scaling
- enabling fast deployment and scalable protection without heavy on-premise infrastructure.
- Automatic updates ensure endpoints are consistently protected
- Uses AI and machine learning to identify and block malware, zero-day attacks, and sophisticated threats in real-time.
- Behavioural analysis helps defend against advanced persistent threats beyond traditional signature-based antivirus
- Simple, unified console for monitoring, alerts, policy management, and deployments across all endpoints
- High reviews and industry scores
Potential Downsides
- High Cost
- Limited Customisation in Some Areas
- Reporting is sometimes criticised as not being detailed enough
- Integration with other security tools is challenging
Best suited for
CrowdStrike is best for enterprise-level organisations that operate across many devices and cloud environments, and want to consolidate multiple security layers into a unified platform.
Data Security Posture Management
DSPM is about the continuous discovery, classification, and risk monitoring of sensitive data. A DSPM platform can tell you where your sensitive data is, how it’s protected, who can access it, and everything else about data compliance.
Forcepoint
“Forcepoint DSPM uses proprietary AI Mesh technology to identify and categorize high-risk data, displaying real-time insights including scan status, performance metrics and audit log visuals.” – Forcepoint
Key Benefits:
- Strong hybrid coverage across cloud, SaaS and on-prem
- Deep integration with Forcepoint DLP, CASB and DDR
- Mature AI classification and guided remediation workflows, leveraging AI Mesh for content and context accuracy
- Automated compliance reporting for audits and oversight
- Extends DSPM controls to AI systems, helping prevent sensitive data from leaking into training sets or prompts
Potential Downsides
- May feel broader than necessary for organisations seeking a narrow, single-purpose DSPM tool
- Pricing:
- Request a demo to learn more: https://www.forcepoint.com/form/demo-request
- Who the tool is best for:
- CISOs seeking a single DSPM tool that covers multi-cloud, SaaS and on-prem environments with tight integration across Forcepoint’s data security ecosystem.
- Perfect solution for teams challenged by:
- Large amounts of shadow data
- Over-permissioned data
- GenAI data leakage risks
- Unidentified data locations
SIEM
Security Information and Event Management platforms collect logs and events from across your systems and analyse them to detect threats. You can’t secure what you can’t see, but with modern workflows jumping between cloud, SaaS, and remote work, logs are everywhere. Some serious software is needed to make sense of this.
Splunk
Splunk is the leading AI-driven security and observability platform, with incredibly strong log analysis tools.
Key Benefits
- Powerful Real-Time Data Collection & Analytics
- Splunk excels at collecting and indexing machine-generated data (logs, events, metrics) from nearly any source, enabling deep analysis and operational intelligence.
- Good Scalability
- Flexible, supporting cloud, on-premises, and hybrid setups
- Strong Search & Query Capabilities
- Customizable dashboards & Visualisations
- Over 2000 integrations
Potential Downsides
- High Cost & some licensing complexity
- Can Be Resource Heavy
- Steep learning curve
- Only really useful for data-driven mid-size and larger businesses with dedicated security teams
Best suited for
Organisations with large volumes of machine data from many sources (servers, network devices, applications, security logs).
Splunk’s scalability, real-time search, and advanced analytics shine where data complexity and volume are high.
Email Security & File Sharing
While the exact numbers vary, studies show that the majority of cyber attacks and data breaches start with an email. All it takes is one slip-up.
Egress
Egress is an email security platform that continuously assesses human risk and dynamically adapts policy controls accordingly.
Key Benefits
Email security
- Uses machine learning to understand human risk
- Alerts and teaches users without interfering with actual business processes
- Both inbound and outbound email protection, stopping accidental or malicious data loss
File Sharing and Collaboration
- Granular controls and customisation
- Full audit trails
- Cloud or hybrid hosting available
- Secure Web Forms for data collection
Potential Downsides
Email security
- slows down communication
- overlaps with existing platforms
- adds user friction
- isn’t a collaboration-native solution
File sharing
Compared to tools like Google Drive or OneDrive:
- Collaboration features are limited
- Not designed for:
- real-time editing
- long-term shared workspaces
- complex permissions over time
- Teams that are already embedded in Microsoft 365 or Google Workspace often see Egress as duplicative rather than additive.
Pricing
There is a free, credit based version. Credits are used up in free-to-free communication. Once you run out of credits, a paid licence costs £90 per email address per year
Best suited for
Medium to large companies with sensitive data that need data loss prevention (DLP), encryption, and insider-risk protection for email and file sharing.
Antivirus & Personal Security
From laptops to mobile phones, every device requires protection. We’ve partnered with TotalAV to offer you award-winning protection at a huge 80% discount for your first year.
TotalAV
“Award-winning antivirus & security software that blocks harmful threats in real-time while also offering WebShield safe browsing, VPN privacy, adblocking, data breach monitoring and password protection across devices” – Jake Dean, TotalAV
Key Benefits
- Strong real-time malware protection and high detection rates.
- Easy-to-use, beginner-friendly interface across Windows, Mac, Android & iOS.
- Includes useful extras beyond antivirus – VPN, password vault, WebShield safe browsing.
- System optimisation tools (junk cleaner, startup manager).
- Competitive introductory pricing and a 30-day money-back guarantee.
- Cross-platform and multi-device support (up to 8 devices on higher plans).
Potential Downsides
- Only really for individual protection – not organisational use
Pricing
Standard Pricing
- Free for basic anti-virus
- TotalAV Premium: £99/yr
- TotalAV Internet Security: £129/yr
- TotalAV Total Security: £149/yr
TotalAV is also one of the only antiviruses that offers premium mobile protection, available for both iOS and Android.
- $1.99 for the first month then $9.99 every month after
MeasureMinds 1st Year 80% Discount
- TotalAV Premium: £19/yr
- TotalAV Internet Security: £39/yr
- TotalAV Total Security: £49/yr
Best suited for
Everyday users & beginners who want simple, broad online protection on multiple devices.
• Budget-minded buyers taking advantage of first-year deals.
• People who want extras bundled in one place (VPN, breach alerts, system tools)
Mobile
Mobile security is often a weak point. If you’ve had any kind of security incident, you need a deep dive into all of your devices.
Certo AntiSpy for iPhone & Android
“Certo AntiSpy bridges the critical gap between basic security apps and professional digital forensics. Because standard iOS apps are ‘sandboxed’—meaning Apple prevents them from scanning other apps or files—we utilize a desktop-based architecture.
By scanning the device via USB, we can analyze the file system from the outside looking in. This allows us to identify deep-rooted threats like hidden spyware, keyloggers, and system tampering that on-device apps from the App Store simply cannot see. It is the only way to get a true forensic-grade audit of an iPhone without handing the device over to an investigator.” – Simon Lewis, Co-Founder, Certo
Key Benefits
- First-of-its-kind complete iPhone spyware detection solution
- Detects commercial spy apps, stalkerware, and monitoring software
- Identifies jailbreaking and OS tampering that compromises security
- Scans for malicious keyboards that can record passwords
- Extremely simple to use – scan completes in minutes
- Affordable alternative to expensive forensic examination services
- Trusted by millions of users worldwide
- Proud partner in Coalition Against Stalkerware
- Makes a real impact for victims of tech abuse and cyberstalking
Potential Downsides
- Requires desktop installation (Mac or Windows computer needed)
- iPhone must be connected via USB cable to perform scan
- iOS-specific solution (separate Android product available)
Pricing
Certo AntiSpy: £7.99/month (3 devices) or £4.17/month billed yearly
Certo AntiSpy Max: £11.99/month (unlimited devices, PDF reports, backup scanning) or £5.83/month billed yearly
30-day money-back guarantee on all plans.
Free versions provided to domestic abuse victims through charity partnerships.
Best suited for
iPhone users concerned about surveillance or stalking, domestic abuse survivors, business professionals worried about corporate espionage, individuals in sensitive relationships, privacy-conscious users who suspect device compromise, and anyone needing affordable iPhone security analysis without paying for expensive forensic services.
Cloud-Native Application Protection Platform (CNAPP)
From CSPM to CWPP, cloud security tool categories seem like an ever-growing list. A CNAPP consolidates all your cloud security needs into a single platform.
Wiz.io
“Wiz was purpose-built for the cloud era from day one. Our CNAPP gives customers the context they need to act fast starting with the Security Graph, which shows how cloud components connect and where the real risks live.
And because Wiz is a single platform, not a patchwork of tools, teams get full visibility and can scale security in step with the pace of innovation. It’s how our customers move faster, stay secure, and work better together.” – Kerry Tuttle, Wiz
Key Benefits
Wiz’s CNAPP gives teams the visibility and context they need to move fast and stay secure. Benefits include:
- One unified platform: Wiz consolidates everything organisations need for cloud security – CSPM, CWPP, vulnerability management, infrastructure-as-code scanning, CIEM, container and Kubernetes security capabilities – into a single, seamless experience. No stitched-together tools or dashboards. Just one platform that gives every team a clear view of risk across code, cloud, and runtime.
- Agentless and agent-based flexibility: Wiz is agentless by design, connecting via API for instant, full visibility across AWS, Azure, GCP, Oracle Cloud Infrastructure, Alibaba Cloud, and Kubernetes with zero impact on performance. When deeper runtime visibility is needed, Wiz also supports agent-based scanning, giving organisations full coverage without compromise.
- Understand real risk: Wiz’s Security Graph maps the entire cloud environment to surface real attack paths. It analyses the relationships between vulnerabilities, misconfigurations, secrets, network exposure, overly permissive identities, and malware, combining them into a single risk queue. This helps organisations focus on what truly matters and avoid unnecessary noise.
- Simplify compliance: Whether it’s FedRAMP, PCI, GDPR, HIPAA, or internal frameworks, Wiz automates compliance checks and pinpoints where sensitive data lives. That enables organisations to move through audits faster and reduce manual work.
- Built-in shift left: Wiz embeds security throughout the development lifecycle, from infrastructure-as-code to production. This gives organisations the ability to catch issues early, resolve them quickly, and keep innovation moving without friction.
Potential Downsides
Based on customer feedback, here are a few areas Wiz is actively addressing:
- Wiz Incident Response (public preview): Helping teams investigate, contain, and recover from cloud security incidents faster.
- Wiz Attack Surface Management (ASM) (public preview): Making it easier to identify and focus on your most critical exposures.
- Extended security graph coverage: Expanding support for SaaS, workloads, and AI infrastructure including Wiz for M365, now in public preview.
- AI-powered agents: Rolling out tools like the SecOps Agent and Issues Agent (both in public preview) to help security teams scale their impact.
Pricing
Wiz offers two pricing plans, priced per workload. There are two additional cost modules, Wiz Code and Wiz Defend that extend its security features. More pricing information can be found here: https://www.wiz.io/pricing
Best suited for
Wiz’s CNAPP is built to support security and development teams across the entire cloud journey, from design to detection to response. Each product is tailored to the people using it, so every team gets exactly what they need.
Wiz Cloud gives CISOs, CIOs, security teams, and developers a shared view of cloud risk. Wiz Code is used by CTOs, AppSec teams, and developers to secure the software development lifecycle. And Wiz Defend is used by SecOps champions, SOC analysts, and incident responders to accelerate cloud detection and response.
MSP Security & Management
A Managed Service Provider remotely manages, monitors, and secures IT infrastructure. They combine proactive IT maintenance (management) with cybersecurity protection (security).
Augmentt
“Augmentt gives MSPs a multi-tenant view of what’s really happening inside Microsoft 365. No guessing, no blind spots; just clear visibility across every client, in a platform that’s actually built to be used every day.” – Derik Belair, Co-founder & CEO, Augmentt
Key Benefits
- Clear visibility into Microsoft 365 users, apps, and settings
- Helps spot security risks and bad settings quickly
- Easy-to-read reports that are client-friendly
- Saves time by reducing manual checks and guesswork
- Built with MSPs with many tenants in mind
Potential Downsides
- Focused mainly on Microsoft 365, not every SaaS app
- Best value comes when used consistently, not just once in a while
Pricing
- Custom pricing based on usage
Best suited for
- MSPs managing Microsoft 365 for multiple clients
- IT teams that want better visibility without added complexity
Secure Code Platform and Training
SecureFlag
“SecureFlag is built for real-world engineering teams, not just compliance checklists. Our platform gives developers hands-on secure coding labs that mirror real vulnerabilities they encounter in production, while giving security leaders measurable insight into risk reduction across teams. Founded by former senior security leaders and trusted by teams in 30+ countries, SecureFlag bridges the gap between security theory and what developers actually ship.” – Owain Powell
Key Benefits
- Hands-on, realistic, secure coding labs (not passive videos or quizzes)
- Covers modern risks, including AI-assisted and AI-generated code vulnerabilities
- Role-based learning paths for developers, AppSec, and security leaders
- Measurable security improvements and reporting for leadership & compliance
- Supports multiple programming languages and frameworks
- Scales well for distributed and international engineering teams
- Used by organisations in 30+ countries
Potential Downsides
- Initial setup and alignment with dev environments can be complex.
- Requires planning and ongoing management to stay relevant.
Pricing
Enterprise SaaS pricing (custom pricing based on team size and requirements)
Best suited for
- Engineering teams building production software
- AppSec and security leaders who want measurable risk reduction
- Organisations moving beyond checkbox compliance toward practical security maturity
- Companies adopting AI-assisted coding that want to reduce new security risks
Network & Internet Intelligence
A new and rapidly growing area of cybersecurity. These are cutting-edge platforms that map external-facing assets, relationships, and infrastructure internet-wide, to reduce risk, enrich alerts, and track potential attacker infrastructure.
Whisper
“Whisper is building the unified nervous system for the internet. We merge internal observability with external intelligence to provide the crucial context that security teams are missing. This allows them to see the entire threat landscape, not just isolated alerts, and move from a reactive to a proactive security posture.
We offer a formidable alternative to traditional threat intelligence tools like DomainTools by providing a much deeper and more connected view of the internet.” – Roman Viliavin, COO, Whisper
Key Benefits
- Unified Visibility: Maps your entire infrastructure and shows you the potential blast radius of any threat.
- High-Fidelity Intelligence: Enriches your SIEM/SOAR tools with clean, real-time data, drastically reducing false positives.
- Efficient Investigations: Streamlines alert triage and investigation, saving your security team valuable time and resources.
- Proactive Defense: Moves you from a reactive to a proactive security posture by connecting the dots between threats and your infrastructure.
- Seamless Integration: Delivers instant data directly into your existing security solutions like Splunk and SentinelOne.
Potential Downsides
- New to the Market: As a newer player, they are still expanding their integration ecosystem.
- Learning Curve: The depth of data and context available may require a learning investment to fully leverage its power.
Pricing
Whisper’s pricing is tailored to the specific needs and scale of each organisation. For a personalised quote, contact their sales team.
Best suited for
Security teams, data privacy managers, and DPOs in mid-to-large enterprises in the UK, US, and EU who are looking to move beyond traditional, reactive security tools and build a proactive, intelligence-driven security program.
AI System Penetration Testing and Defence
Countless businesses are enhancing their products with AI. But adding powerful AI also adds a new world of potential security issues. Issues that existing tools and workflows just aren’t a great fit for.
Mindgard
“Mindgard can test your AI models automatically in the same way a real attacker would, which uncovers the vulnerabilities before they can become actual security problems.” – Fergal Glynn, Mindgard
Key Benefits
- With automated red teaming, you save a lot of time on security testing manually
- This works across multiple AI types including language models, images, and audio
- This shows you exactly where your AI is weak when a real attack happens
- It plugs into your existing development workflow through APIs and command line tools
- It helps you with proving compliance and reduces your overall AI risk
Potential Downsides
- It is built for enterprise use, which might be too much for teams that are smaller
- Its Security features are complex if your team don’t know much about pentesting
Pricing
Based on your needs, it has custom quote for both Labs tier and Enterprise tier
Best suited for
This is best for enterprise level security teams that manage AI deployments, machine learning engineers who need continuous security validation, and DevSecOps professionals who are building compliant AI systems.
Offline AI
The best defence can be to simply make yourself unattackable. That’s the idea behind this “Anti-SaaS” tool, for those who want to leverage the power of AI without risking any data leaks.
The Burritt Center
“In this age of endless data hacks, the safest AI is one that literally can’t connect to the web. We created the Burritt Center AI to let execs and privacy pros harness top-tier LLMs without a scrap of data ever escaping their machine. Forget encryption—it’s all about total physical separation.” – Ken Rheingans, Founder, The Burritt Center
Key Benefits
- No Chance of Data Leaks: It’s completely air-gapped, so remote hacks are out of the question.
- Full Control Over Your Data: Nothing gets sent over the net or any network.
- Skip the Subscription Hassle: Buy it once and it’s yours for good.
- Easy Setup: Just plug in the external SSD and run it on your everyday PC—super BYOD-compatible.
Potential Downsides
- Tied to Your Hardware: Performance hinges on your computer’s RAM and CPU power.
- No Real-Time Web Access: It won’t pull in live news or search the internet (that’s the point, after all).
Pricing
- Basic: $295 (one-time fee)
- Pro: $495 (one-time fee)
Best suited for
DPOs, executives dealing with confidential IP, preppers, or anyone who requires AI help but can’t risk—or isn’t allowed to—send data to the cloud.
Compliance & ISMS Automation
Information security and data privacy compliance are subjects close to our hearts at MeasureMinds.
Kertos
“Most information security and data privacy compliance platforms were built with focus on North American regulations, then adapted for Europe. Kertos is the opposite: the software is purposefully built for European frameworks like NIS2, DORA, ISO, GDPR, and the EU AI Act on top of SOC2 and others.
Customers get certified in two to six weeks instead of months, without the hassle of managing data across different platforms or documents or facing high costs linked to external consulting agencies.
Compliance is maintained overtime on autopilot thanks to a centralized system for risk management, incident management, training, IT security, policy management, vendor management, automated DSR processing, and more.” – Andy Mura, Kertos
Key Benefits
- Platform-first approach combined with 1:1 guidance and support through a team of infosec and data privacy experts
- A single centralised space to manage all compliance and IT security topics and audits
- Six-week average implementation time with 100% audit success rate- 80% reduction in compliance effort through automation and 100+ native integrations
- KAIA, a proactive AI-powered compliance assistant available 24/7 for workflow automation, policy generation, and more
- 70% framework overlap means existing certifications accelerate new ones
Potential Downsides
- Strongest fit for companies headquartered in Europe or companies that operate in the territory (or plan to enter the market)
- Platform-first approach requires software adoption rather than pure consulting engagement- Most effective for companies with an existing digital infrastructure
- Not set up to fully cater to organisations that work in the health industry yet
Pricing
Starts at approximately $600/month for core compliance modules. Enterprise and multi-framework bundles available. No hourly charges for consulting.
Best suited for
Startups and scale-ups that want to attract the interest of larger customers, partners, or investors or that operate in a market with high pressure when it comes to data privacy and information security and want to effectively achieve compliance and certifications.
Larger organisations in highly regulated markets that require a constant high level of compliance while demonstrating adherence to main directives and regulations, also when it comes to AI governance and security.
- Enterprise SaaS SEO – Expert Strategies, Tools, & Playbooks - 31/03/2026
- How to Set Up and Implement Cookiebot by Usercentrics - 18/03/2026
- Top 5 OneTrust Alternatives for 2026 - 12/03/2026
